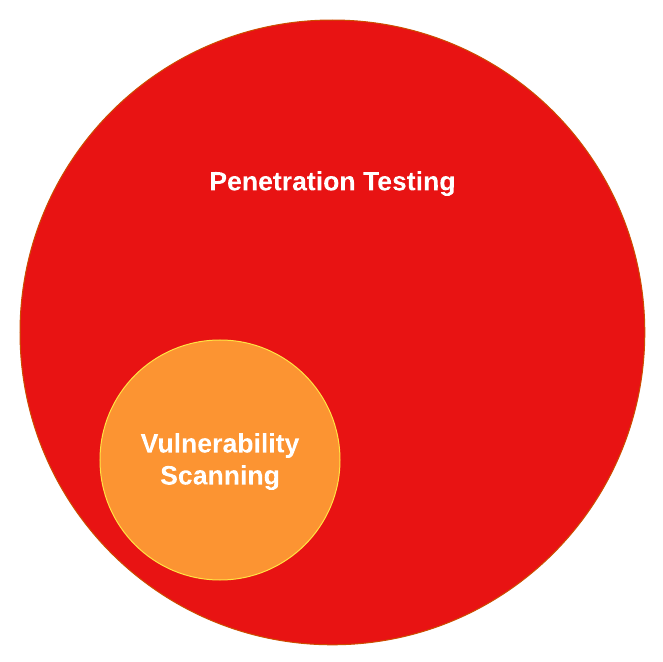
Vulnerability scanning and penetration testing are two complementary techniques that aim to answer the same question: Where am I vulnerable and what should I do about it?
While both techniques are often confused as being the same thing, they are very different in what they do and how you should use them.
What is vulnerability scanning?
Vulnerability scanning is the use of automated tools to evaluate IT Systems for known vulnerabilities – things which can be exploited to cause harm to a computer or its users. These tools work by identifying available software services, comparing their version numbers (if visible) against vulnerability and patch release databases, and testing for common misconfiguration and default passwords.
Because vulnerability scanning is performed by automated scanners it can be performed as frequently as you wish.
What is penetration testing?
Penetration testing or pen testing goes a step further than vulnerability scanning and actively attempts to exploit flaws or vulnerabilities in IT Systems to achieve a defined goal. This could be something simple such as a simulated defacement of a website or something more complicated such as the simulated theft of sensitive data and a ransomware attack against a company.
While vulnerability scanning generally uses automated tools, penetration testing is generally a manual process executed by highly skilled penetration testers. Pentesters may use vulnerability scanners to identify possible attack paths but this is only the start of their process.
The real value of a penetration test comes from the skills and experience of the penetration tester looking at your IT systems. Most real cyber attacks chain several weaknesses together in order to achieve their goal. An unpatched web server may be detected by a vulnerability scanner but that same scanner won’t exploit it and pivot into your internal network to tell you what other problems it can see.
The main difference between a vulnerability scan and a penetration test is this: a vulnerability scan will tell you what problems you might have; a penetration test will show you how you’re actually going to be hacked.
Benefits of a Vulnerability Scanning
Just because they don’t simulate a real cyber attack doesn’t detract from the effectiveness of a solid vulnerability scanning process. As these tools are automated you can run them as often as you wish. With enough scanning resources, you can perform vulnerability scans daily, hourly, or almost continuously which is very useful for environments running with continuous integration and delivery (CI/CD).
Vulnerability scanners are much cheaper than penetration testing. A good penetration tester will usually bill at over £1,000 per day and, depending on how big your organisation is, the overall test will run for days or even weeks. Once a vulnerability scanner is licensed, and there are many excellent free-to-use vulnerability scanners, the only ongoing costs and the servers from which they run.
Limitations of Vulnerability Scanning
Vulnerability scanners can only report on what they observe. Not all findings reported by a vulnerability scanner will be valid. False positives, while uncommon, can be raised by vulnerability scanners and will appear in reports as things you need to fix when in reality, you don’t. A penetration tester will validate all findings before reporting them to you. For that reason, vulnerability scanners generate noise that you must filter out on your own.
Vulnerability Scanning vs Penetration Testing
One of the core cyber security principles is defence in depth. Rather than comparing the two and trying to weigh one against the other, the best solution is to embrace both and implement continuous vulnerability scanning of all of your assets and supplement it with regular penetration testing.
Use the cheaper, automated vulnerability scanning to identify and resolve easy-to-find issues. Use the more expensive manual penetration testing to look for and fix more complex problems that vulnerability scanners miss. The more low-hanging vulnerabilities a penetration tester finds the more time they’ll spend validating and writing them up instead of digging deeper for high-impact vulnerabilities
Vulnerability Scanners
There are a lot of excellent vulnerability scanners available – here are some of my personal recommendations:
- Nessus – One of the original and the best vulnerability scanners
- Tenable.io – Cloud-based vulnerability management powered by Nessus
- PingCastle – A vulnerability scanner for Active Directory
- OpenVAS – An open-source vulnerability scanner, similar to Nessus
- Burp Suite – Web application vulnerability scanner and intercepting proxy
- Nuclei – A fast and customisable vulnerability scanner you can tailor for your own applications, environment, and zero-day vulnerabilities
- WPScan – WordPress powers 64% of the web. This scanner is dedicated to finding vulnerabilities in your own deployments
- Nmap – A very lightweight network and vulnerability scanner, customisable with nmap scripts both from the community library and with your own bespoke scripts

Leave a Reply